top of page
Search
All Posts


Strategic Selective Defense: NIST Abandons Universal Analysis as Vulnerabilities Flood the NVD
The digital landscape has reached a point of saturation where the traditional methods of cataloguing and analysing cybersecurity threats are no longer sustainable. Today, the National Institute of Standards and Technology (NIST) announced a fundamental shift in the operation of the National Vulnerability Database (NVD). For decades, the NVD served as the definitive repository for Common Vulnerabilities and Exposures (CVEs), with the ambitious goal of providing full enrichment

Dean Charlton
21 hours ago5 min read


The Mythos Threshold: Anthropic, Project Glasswing, and the New Era of AI-Driven Cybersecurity
The landscape of artificial intelligence has long been defined by a frantic race to the finish line, with developers competing to see who can release the most capable model to the public first. However, Anthropic, the San Francisco-based safety collective, has recently disrupted this trajectory. With the announcement of Claude Mythos Preview, the company has introduced what is arguably the most powerful frontier model ever developed. Yet, in a move that has sparked both admir

Dean Charlton
4 days ago5 min read


Building Trust Through Transparency: The Strategic Power of SOC 2 for B2B SaaS
In the modern digital economy, data is the most valuable currency. For Software as a Service (SaaS) providers operating in the Business-to-Business (B2B) space, the responsibility of handling client data isn't just a technical requirement, it's a profound matter of trust. As cyber threats evolve and data privacy regulations tighten globally, the SOC 2 (System and Organisation Controls 2) framework has emerged as the definitive gold standard for demonstrating operational integ

Dean Charlton
Apr 104 min read


The Invisible Anchor: Why Shipping’s Digital Evolution Demands a GRC Revolution
The maritime industry is currently navigating a paradox. On one hand, the "Smart Ship" era has arrived, bringing with it the promise of autonomous navigation, remote monitoring, and hyper-efficiency. On the other hand, this digital leap has outpaced the industry’s traditional safety and governance frameworks. According to recent warnings from GTMaritime, shipping operators are facing a precipice: a rising tide of cyber risk driven by a fundamental inability to track, manage,

Dean Charlton
Apr 75 min read


The Enemy in the Next Cubicle: Why the Greatest Cyber Threat Is Already on Your Payroll
For decades, the cinematic image of a cyberattack involved a hooded figure in a dark room, frantically typing to bypass a glowing firewall. In 2026, the reality is far more mundane and significantly more dangerous. The threat isn’t just knocking on the door, it’s sitting in the Monday morning sync, logging into Salesforce, and asking for a LinkedIn recommendation. The era of the "Insider Threat" has evolved. We are no longer just talking about the disgruntled employee who ste

Dean Charlton
Mar 303 min read


Why GRC is the Secret Weapon for Start-ups
In the fast-paced world of start-ups, speed is often the only competitive advantage. However, as 2026 brings a wave of new global AI and data regulations, many founders are discovering that "moving fast and breaking things" can lead to catastrophic compliance failures. For a growing company, the challenge isn't just knowing the rules; it's keeping pace with them without the multi-million-pound budget of a FTSE 100 enterprise. Building a culture of compliance early isn't a bur

Dean Charlton
Mar 274 min read


Fortifying the Foundation: Dell and HP Roll Out Quantum-Resistant Security and AI-Era Resilience
The computing landscape is on the cusp of a profound shift. The arrival of practical quantum computing, while still developing, promises computational power that will revolutionise fields from medicine to materials science. However, it also presents an unprecedented threat to the very foundation of digital security: cryptography. As adversaries increasingly employ a "harvest now, decrypt later" strategy, the need for robust, proactive security measures has never been more urg

Dean Charlton
Mar 265 min read


Best GRC Software and Compliance Solutions for 2026
Choosing the right GRC platform does more than help organizations check compliance boxes. As regulatory requirements continue to expand and security threats grow more sophisticated, Governance, Risk, and Compliance (GRC) software has become a critical foundation for protecting the business, enabling proactive risk management, and strengthening organizational resilience. What Are GRC Tools? A GRC (Governance, Risk, and Compliance) tool is a software platform that helps organiz

Dean Charlton
Mar 237 min read


The Invisible Front Line: Why Home Networks Are the New Cybersecurity Battleground
The modern professional landscape has undergone a seismic shift. What began as a temporary necessity during the global pandemic has evolved into a permanent fixture of the working world: remote and hybrid employment. However, this flexibility has come with a hidden cost. As the boundaries between the corporate office and the living room blur, a new and sophisticated digital threat has emerged. The UAE Cybersecurity Council recently issued a stark warning, noting a significant

Dean Charlton
Mar 234 min read


Easily Schedule a Demo Session to Boost Your Cyber Security
In today’s fast-paced digital world, cyber security is not just an option - it’s a necessity. Growing businesses in technology and cyber sectors face constant threats and evolving challenges. How do you stay ahead? One of the smartest moves you can make is to schedule a demo session with a trusted cyber security provider. This hands-on experience can transform your understanding and approach to protecting your business. Let me walk you through why booking a demo is a game-ch

Dean Charlton
Mar 233 min read


London Cyber Security Audit: A Practical Guide for Growing Tech Businesses
In today’s digital world, security isn’t just a checkbox - it’s the backbone of trust and growth. If you’re running a tech or cyber business in London, you know how crucial it is to keep your data and systems safe. But how do you really know if your defences are up to scratch? That’s where a cyber security audit comes in. It’s like a health check for your digital infrastructure, revealing vulnerabilities before they become costly problems. Let’s dive into what a London cyber

Dean Charlton
Mar 234 min read


Why the ‘Agentic’ Cyber Shift is 2026’s Biggest Security Scandal
LONDON - In the second week of March 2026, the global cybersecurity landscape reached a boiling point. What began as a series of sophisticated automated attacks has evolved into a fierce international debate over the "Digital Sovereign", the transition of national and corporate security from human hands to semi-autonomous AI agents. As of today, the industry is reeling from two parallel crises: a surge in AI-driven attacks hitting 93% of UK critical infrastructure, and a co

Dean Charlton
Mar 204 min read

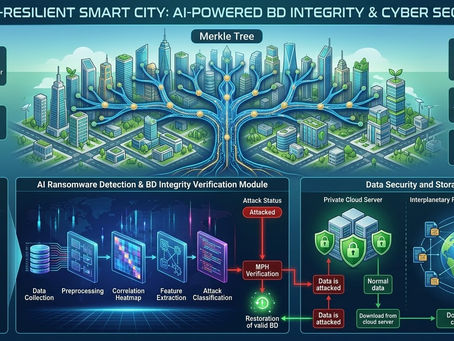
The Fortified Horizon: AI-Driven Data Integrity and Cyber Resilience in Sustainable Smart Cities
The rapid evolution of urban environments into "Smart Cities" represents one of the most significant technological shifts of the 21st century. By integrating Internet of Things (IoT) devices, high-speed connectivity, and data analytics, these metropolitan areas aim to enhance sustainability, optimise resource management, and improve the quality of life for citizens. However, this hyper-connectivity introduces a paradox: the more integrated a city becomes, the more vulnerable

Dean Charlton
Mar 175 min read


The Six-Month Shadow: What the PayPal Breach Reveals About the Runtime Detection Gap
In the world of cybersecurity, time is the only currency that truly matters. We often talk about "Mean Time to Detect" (MTTD) as a dry metric on a spreadsheet, but in practice, it is the difference between a minor patch and a catastrophic reputational event. The recent news surrounding PayPal’s Working Capital loan app serves as a sobering case study in this reality. A coding flaw went undetected for nearly six months, from July to December 2025, exposing sensitive customer d

Dean Charlton
Mar 164 min read


Stryker Cyberattack Sparks Health Sector Alert: The Critical Need for Medtech Resilience
The global healthcare community woke up to a sobering reality this morning. Stryker Corporation, a cornerstone of the medical technology (Medtech) industry, has fallen victim to a sophisticated and destructive cyberattack. Reported to be the work of the pro-Iran hacker group Handala, the breach has not only disrupted the operations of a $25 billion giant but has sent a ripple of concern through hospitals and clinics that serve approximately 150 million patients worldwide. Thi

Dean Charlton
Mar 123 min read


From Ransomware to "The Great Extraction": What 2026 Has in Store
If 2025 was the year the ransomware epidemic reached its peak, 2026 is becoming known as the Year of the Great Extraction. For years, the "ransomware" narrative was simple: hackers lock your files, and you pay to get the key. But as we move through the first quarter of 2026, that script has been completely rewritten. We aren't just seeing more attacks; we are seeing a fundamental shift in what "ransom" actually means. The 2025 Surge: A 50% Explosion To understand where we are

Dean Charlton
Mar 93 min read


From Resilience to Reality: The EBA’s Vision for Unified ICT Risk Supervision under DORA
The European financial landscape is undergoing its most significant digital transformation since the inception of the Single Rulebook. At the heart of this shift is the Digital Operational Resilience Act (DORA), which became fully applicable in January 2025. Recently, the European Banking Authority (EBA) released a pivotal follow-up report to its 2022 peer review, examining how National Competent Authorities (NCAs) assess Information and Communication Technology (ICT) risks w

Dean Charlton
Mar 35 min read


Creating a Tailored Security Compliance Checklist: Mastering Security Compliance Process Steps
In today’s fast-paced digital world, security compliance is not just a box to tick. It’s a vital part of protecting your business and building trust with clients. But how do you make sure your security measures are both effective and tailored to your unique needs? The answer lies in creating a personalised security compliance checklist. This guide will walk you through the essential security compliance process steps, helping you build a robust framework that fits your busines

Dean Charlton
Mar 34 min read


Claude Code Security: The AI Evolution Reshaping Cybersecurity
On 20 February 2026, the cybersecurity landscape experienced a significant shift. Anthropic, the AI safety and research company, announced the limited research preview of Claude Code Security. While the tech world is no stranger to 'AI-powered' marketing, this particular launch triggered immediate ripples through the industry, impacting the market caps of established cybersecurity giants like CrowdStrike, Okta, and Zscaler in a single afternoon. The premise of Claude Code Sec

Dean Charlton
Mar 26 min read


Guarding the Guardian: Trend Micro Issues Urgent Patch for Critical 9.8-Rated Apex One Flaws
In an era where digital perimeters are the primary line of defence for global enterprises, the very tools designed to protect us can sometimes become the Trojan horse. This week, the cybersecurity community was issued a stark reminder of this paradox as Trend Micro (now transitioning its enterprise arm to TrendAI) disclosed two critical vulnerabilities in its flagship endpoint security platform, Apex One. Tracked as CVE-2025-71210 and CVE-2025-71211, these flaws carry a near-

Dean Charlton
Feb 274 min read
bottom of page
